Microsoft Application Inspector Source Code Analyzer
Microsoft has released the Microsoft Application Inspector, a cross-platform open source (!) tool for analyzing source code.
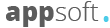
Application Inspector differs from traditional static analysis tools – it does not attempt to identify “good” or “bad” patterns; it will report what it will detect, based on the initial set of more than 500 rule templates for detecting functions, including functions that affect security, such as the use of cryptography, etc.
The main goal of Application Inspector is a systematic and scalable identification of source code functions that are not found in other typical static analyzers. This allows developers and security professionals to verify the intended goals of the components, for example, that the library used does only what is declared in it.
Modern applications rely heavily on software written outside of your company, which carries risks. Application Inspector can help to determine interesting characteristics of the application by examining the source code, saving considerable time compared to the “manual” analysis.
The application is a client tool based on .NET Core, so it will work on Windows, Linux or macOS and does not require elevated privileges, as well as a local database, network communications or telemetry. To start it, simply use the standard dotnet command line to call, for example, dotnet ApplicationInspector.dll if you are running Linux or macOS or Windows AppInspector.exe.
|
1 |
> dotnet AppInspector.dll or on *Windows* simply AppInspector.exe <command> <options> Microsoft Application Inspector 1.0.17 ApplicationInspector 1.0.17 (c) Microsoft Corporation. All rights reserved ERROR(S): No verb selected. analyze Inspect source directory/file/compressed file (.tgz|zip) against defined characteristics tagdiff Compares unique tag values between two source paths tagtest Test presence of smaller set or custom tags in source (compare or verify modes) exporttags Export default unique rule tags to view what features may be detected verifyrules Verify rules syntax is valid help Display more information on a specific command version Display version information |
You can add / edit / delete standard rules or patterns as needed. It is also possible to add your own rules to a separate path to the default set and save the default set or exclude them using command-line options.
Areas of testing and application:
- Control Flow: Dynamic Code Execution, Process Management.
- Cryptography: Encryption, Hashing, Secrets, Randomization.
- OS Operations: File System ,Environment Variables, Network Operations, User Accounts, Windows Registry.
- Data: JSON/XML, Secrets/Access Keys, Sensitive Personal Data, SQL/ORM.
- Data Handling: Object Serialization (XML/JSON), Flash, PDF, Silverlight, Audio/Video Media Use or Parsing, Bluetooth, Cellular, RPC.
- Frameworks: Development, Testing, Dependencies.
By default, the Application Inspector generates an html-based report to illustrate features, a project summary, and metadata found. JSON and TEXT output format options are also supported.
Related Posts
Leave a Reply Cancel reply
Service
Categories
- DEVELOPMENT (123)
- DEVOPS (54)
- FRAMEWORKS (46)
- IT (25)
- QA (14)
- SECURITY (15)
- SOFTWARE (13)
- UI/UX (6)
- Uncategorized (8)