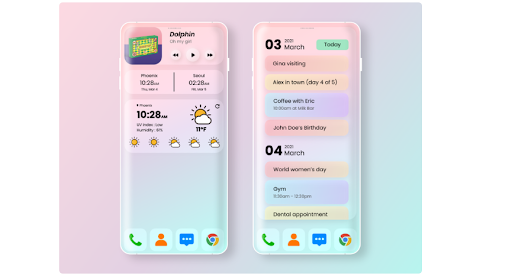
Discover the Top 10 Tools for Mobile Application Development
In today’s digital era, mobile applications have become indispensable for businesses and individuals alike. With the ever-increasing demand for innovative and user-friendly mobile apps, developers are constantly seeking tools and technologies to streamline the app development process. In this article, we’ll explore the top 10…
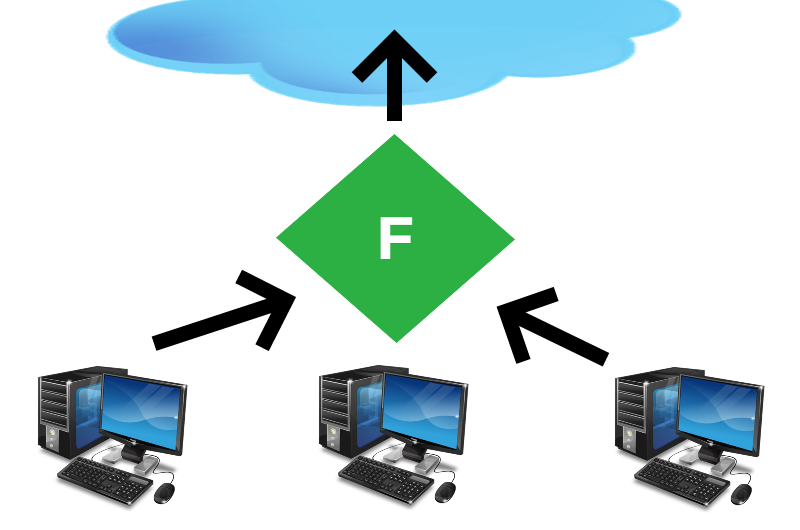
Implementing messaging via MassTransit
Implementing messaging via MassTransit Sooner or later, many projects are faced with the problem of messaging. Often messages must be exchanged between elements of distributed systems using different approaches and technologies. In modern systems, to solve this problem, as a rule, message buses are used,…
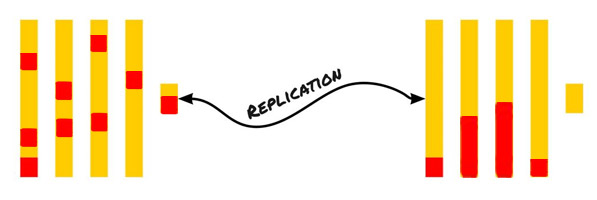
ClickHouse replication: expectation and reality
There is a lot of different information about ClickHouse, but let’s talk about how to prepare the infrastructure with it. It took us about six months to get it to work exactly the way it finally suits us. It was necessary to find an efficient…
Update Tuesday: Microsoft has released August security updates
Microsoft released planned security updates covering 44 vulnerabilities (51 vulnerabilities, including closed vulnerabilities in Microsoft Edge browser), 7 of which were classified as critical, 3 were of the zero-day (0-day) vulnerability, and 1 vulnerability was exploited in real attacks. In this article, I will cover…
Fiddler = convenient sniffer + proxy server
In this article, we will understand how and why you can change HTTP packets when sending to the server and when receiving responses from the server. Why do this? Example 1. Traffic analysis.Your network users are using your proxy server. You can see which sites…
Linux & Desktop – how to live and survive
Many people, when they hear that someone is using Linux as a workstation, ask themselves why and how we do it. If there are many very different options for the first question, then the experience with the second one is quite similar for generalization. How…
How can you save money on mobile development?
Any application consists of two basic components – design and functionality. The good news is that you can save on both. Saving on functionality There is such a thing called MVP – Minimum Viable Product. You have a super idea. Delivery of oranges. You are…
VMware App Control. How to protect End-of-Life operating systems if there is no way to replace them
Attacks such as WannaCry and Petya / NotPetya have demonstrated that hackers are more familiar with the vulnerabilities of your unsupported systems than you are. When new fixes are released for new systems, attackers can easily reverse engineer the update and quickly discover any weaknesses…
11 mobile development trends in 2020
Mobile platforms are evolving and exploring themselves. The mobile app market should grow by 385% by 2021. In 2021, there will be about 7 billion mobile device users in the world. By 2022, the costs of users in the App Store will increase by 92%…
What is the difference between a template solution and custom development?
It is difficult to choose between a template and a unique website: from the one side, you want a truly exclusive product, but from the other, you save money by ordering something simpler. Before making a final decision, you should understand what is what in…
Service
Categories
- DEVELOPMENT (123)
- DEVOPS (54)
- FRAMEWORKS (46)
- IT (25)
- QA (14)
- SECURITY (15)
- SOFTWARE (13)
- UI/UX (6)
- Uncategorized (8)