VMware App Control. How to protect End-of-Life operating systems if there is no way to replace them
Attacks such as WannaCry and Petya / NotPetya have demonstrated that hackers are more familiar with the vulnerabilities of your unsupported systems than you are. When new fixes are released for new systems, attackers can easily reverse engineer the update and quickly discover any weaknesses in your end-of-life (EOL) systems. Traditional security solutions are powerless to detect and prevent complex attacks and unknown threats.
These systems often perform important business functions, access sensitive data, and place high demands on performance and availability. This all makes it difficult to update or replace them when vendors drop security support. As a result, they are ideal targets for hackers to exploit because of the sensitive information they can store and the difficulty of protecting them with updates.
In addition to security threats, many of the regulations and standards that organizations must follow to ensure security and comply with data privacy laws provide for stringent levels of security that EOL systems simply cannot meet. When systems go to EOL, they can be easily compromised due to lack of patch management or effective endpoint protection.
Vulnerabilities exist on systems that will never be patched. This is a critical area of focus for Compliance Officers because of the significant risk that the organization assumes by continuing to operate them.
Compensating controls for protecting EOL systems from heightened liability and threats
There are compensating controls that businesses can implement to help reduce the liability associated with using EOL operating systems and keep them secure. Some of the key techniques are network isolation/segmentation, virtualization, and application control / whitelisting.
Network isolation / segmentation
One option for securing EOL devices is to place critical servers on an isolated network to ensure that devices cannot communicate with any machines outside of the network or connect to the Internet. By isolating the network, EOL devices are protected from threats, but severely restricts access to other critical resources, including Internet and cloud functionality. While this security model can be used as a compensating control to mitigate threats, it can disrupt business and impact end-user productivity, as most mission-critical applications on servers must be connected to corporate servers for employee access.
Virtualization
Hosting hosts in a virtualized environment can provide a number of security benefits: improved control over critical hosts, ease of reimaging in the event of a compromise, and the ability to limit exposure to critical servers. Once a host is targeted, it can be quickly isolated and reinitialized, but for mission-critical servers running applications that require 24/7 access, virtualization presents an opportunity for increased administration and resources. It can also cause compliance policies to fail because the data must be controlled or cannot run in a virtual environment.
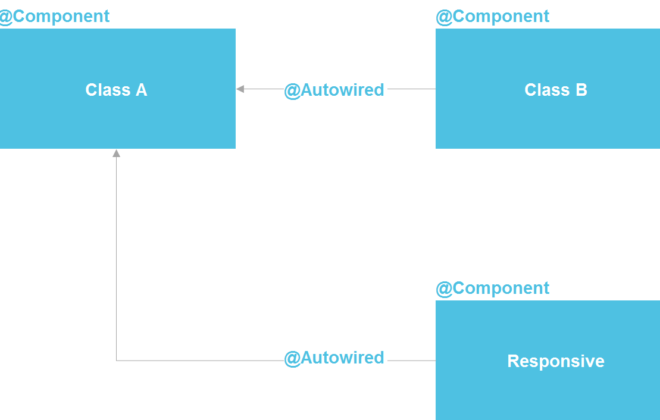
Application control and whitelisting
Australian Signals Directorate’s Essential Eight (ASD) has named the whitelist as the number one application protection model, which is a security model that allows known “good” applications to run rather than blocking known “bad” ones. By allowing only trusted software to run, the application whitelist stops exploits and reduces administration associated with system and application patches and updates. In a “fail-by-default” mode, the application whitelist is a highly effective compensatory control that meets regulatory compliance standards and protects legacy systems.
Proven effectiveness of security and compliance controls
Coalfire, an independent qualified security assessment firm, has tested and determined that VMware App Control can provide the flexibility to enable, manage, and meet PCI DSS requirements in areas such as file integrity monitoring / control, change and alert monitoring, and audit preservation. …
The solution can also:
- Support the development of a combination of direct and compensatory control for requirements such as antivirus and patch management (protection of non-upgraded systems).
- Maintain ongoing compliance for key structures including PCI-DSS, ASD, GDPR, FISMA, NIST, Singapore MAS and many more.
Provide:
- Monitor critical activity and provide configuration to assess risk and maintain system integrity.
- Security of EOL systems with powerful change control and whitelisting policies.
Carbon Black protects servers and critical / EOL systems with 100% efficiency. VMware App Control is trusted by over 2,000 organizations, including over 25 Fortune 100 organizations, to protect their enterprise endpoints and servers. It is a proven solution that you can implement to keep your devices safe at end-of-life.
Best protection
VMware App Control was the only solution to stop 100% of attacks in the NSS Labs 2017 Advanced Endpoint Protection (AEP) benchmark.
This is possible thanks to its features such as:
- Blocking Systems: Stopping Malware, Ransomware and Zero-Day Attacks
- Blocking unauthorized changes: built-in file integrity monitoring, device management and memory protection
- Protecting mission-critical systems: support for embedded, virtual and physical OS
High performance
VMware App Control is a proven and scalable application management solution. A single administrator can manage over 10,000 systems, giving security teams complete control with minimal effort.
- Out-of-the-box templates reduce management overhead
- Built-in workflow and automation mechanisms help speed up implementation
- Cloud-based reputation for fast decisions on reliable software.
Related Posts
Leave a Reply Cancel reply
Service
Categories
- DEVELOPMENT (123)
- DEVOPS (54)
- FRAMEWORKS (46)
- IT (25)
- QA (14)
- SECURITY (15)
- SOFTWARE (13)
- UI/UX (6)
- Uncategorized (8)