Update Tuesday: Microsoft has released August security updates
Microsoft released planned security updates covering 44 vulnerabilities (51 vulnerabilities, including closed vulnerabilities in Microsoft Edge browser), 7 of which were classified as critical, 3 were of the zero-day (0-day) vulnerability, and 1 vulnerability was exploited in real attacks. In this article, I will cover the highlights of the August update release.
Remember, almost 90% of all vulnerabilities already had patches from the manufacturers at the time of their release , so it is so important not only to update your software but also to do it in a timely manner.
– Vulnerability Review Report by Flexera
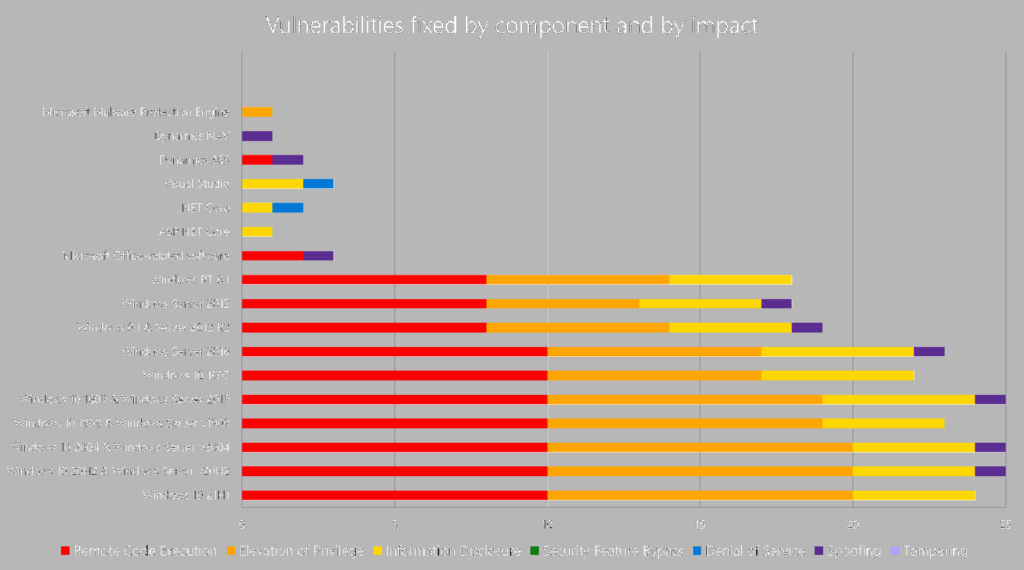
A summary of the number and type of vulnerabilities in the respective products is shown in the graph.
The following vulnerabilities and security updates should be particularly noted
CVE-2021-34535 – Remote Desktop Client Remote Code Execution Vulnerability (Critical, CVSS Score 8.8)
CVE-2021-26432 – Windows Services for NFS Remote Code Execution Vulnerability (Critical, CVSS Score 9.8)
CVE-2021-26424 – Windows TCP/IP Remote Code Execution Vulnerability (Critical, CVSS Score 9.9)
CVE-2021-34480 – Scripting Engine Memory Corruption Vulnerability (Critical Remote Code Execution, CVSS Score 6.8)
CVE-2021-34478 – Microsoft Office Remote Code Execution Vulnerability (Important Remote Code Execution, CVSS Score 7.8)
CVE-2021-36941 – Microsoft Word Remote Code Execution Vulnerability (Important Remote Code Execution, CVSS Score 7.8)
The following vulnerabilities have been publicly disclosed:
CVE-2021-36934 – Windows Elevation of Privilege Vulnerability (Important, CVSS Score 7.8)
CVE-2021-36942 – Windows LSA Spoofing Vulnerability (Important, CVSS Score 7.5)
This vulnerability is exploited in an attack dubbed PetitPotam. To fully mitigate the vulnerability, in addition to installing the update, you must configure it according to the instructions in article ADV21003 Mitigating NTLM Relay Attacks on Active Directory Certificate Services (AD CS).
The exploitation of the following vulnerabilities has been documented in real attacks:
CVE-2021-36948 – Windows Update Medic Service Elevation of Privilege Vulnerability (Important EOP, CVSS Score 7.8)
CVE-2021-36936 – Windows Print Spooler Remote Code Execution Vulnerability (Critical, Publicly Disclosed, CVSS Score 8.8)
CVE-2021-36947 – Windows Print Spooler Remote Code Execution Vulnerability (Important, CVSS Score 8.8)
CVE-2021-34483 – Windows Print Spooler Elevation of Privilege Vulnerability (Important, CVSS Score 7.8)
These vulnerabilities affect all versions of Windows and Windows Server. One of the vulnerabilities is Critical and has been publicly disclosed. It should be noted that after installing the security update, the default behavior of the Point and Print function changes – now only users with administrative accounts can install and update printer drivers. Details can be found on our blog.
Don’t forget about servicing stack updates
Servicing Stack Updates (SSUs) were released in August for the following operating systems:
- Windows 10 version 1809, 1909, 2004, 20H2, 21H1
- Windows Server 2019 version 1909, 2004, 20H2
For Windows 10 and Windows Server 2004 and 20H2, SSUs are now shipped in a Unified monthly update along with the rest of the updates.
Related Posts
Leave a Reply Cancel reply
Service
Categories
- DEVELOPMENT (123)
- DEVOPS (54)
- FRAMEWORKS (46)
- IT (25)
- QA (14)
- SECURITY (15)
- SOFTWARE (13)
- UI/UX (6)
- Uncategorized (8)