Complex commercial products for Kubernetes Security
Aqua security
Website: www.aquasec.com
License: commercial
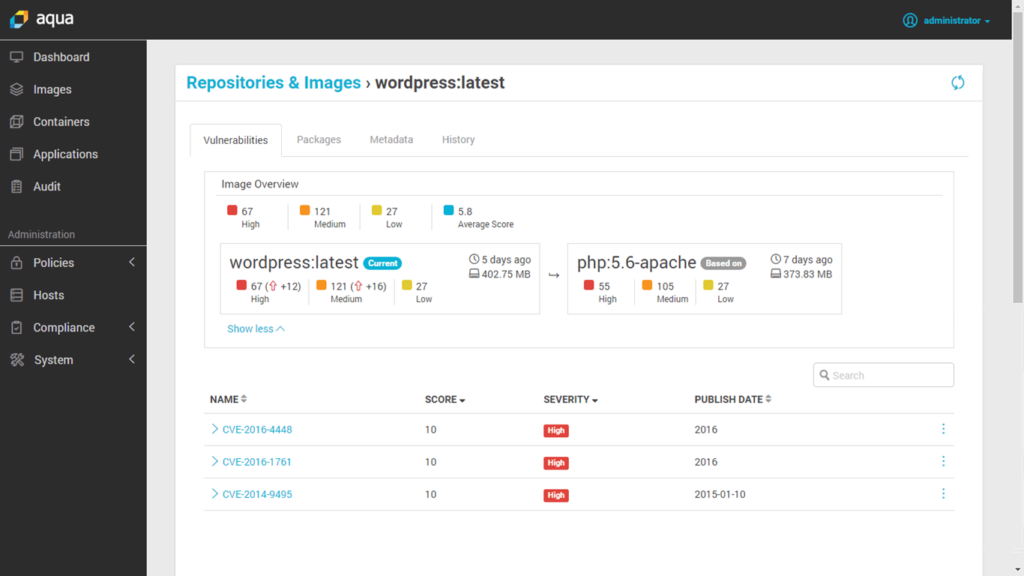
This commercial tool is designed for containers and cloud workloads. It provides:
- Image scanning integrated with the container registry or CI / CD pipeline;
- Runtime protection with the search for changes in containers and other suspicious activity;
- Native container firewall;
- Security for serverless in cloud services;
- Compliance and auditing combined with event logging.
Capsule8
Website: capsule8.com
License: commercial
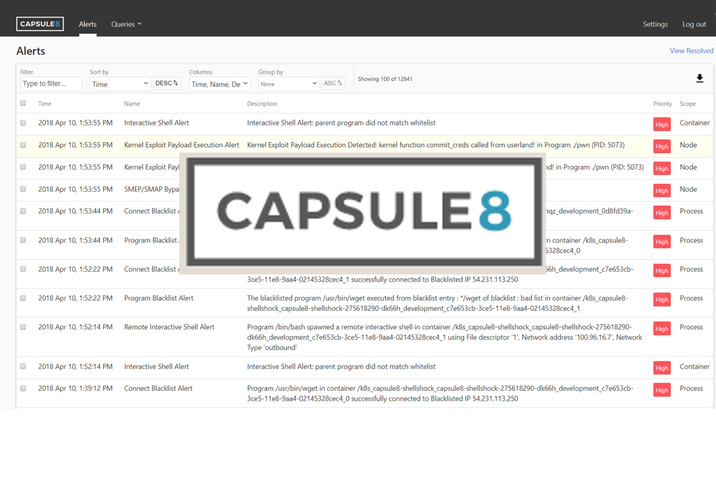
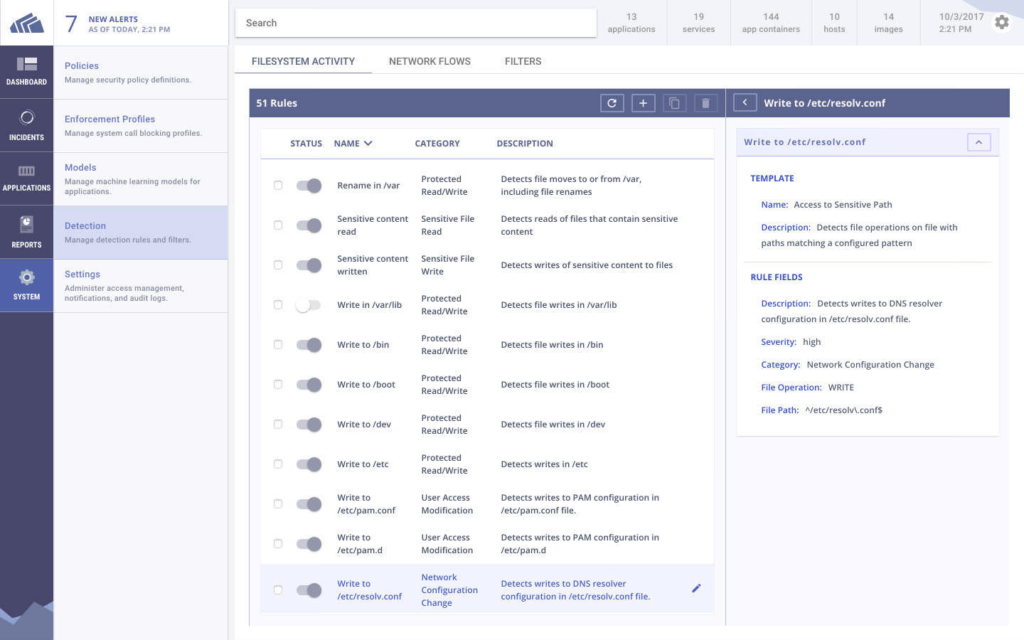
Capsule8 integrates into the infrastructure by installing the detector in a local or cloud Kubernetes cluster. This detector collects telemetry of the host and network and correlate it with various types of attacks.
The Capsule8 works on early detection and prevention of attacks that use fresh (0-day) vulnerabilities. Capsule8 can upload updated security rules directly to the detectors in response to recently discovered threats and software vulnerabilities.
Cavirin
Website: www.cavirin.com
License: commercial
Cavirin acts as a counteragent on the company side for various departments, which are involved in safety standards. It can not only scan images, but also integrate into a CI / CD pipelines and block images that don’t meet standards, before they get into closed repositories.
The Cavirin Security Suite uses machine learning to assess the state of cybersecurity and offers tips for increasing of security and improving compliance with security standards.
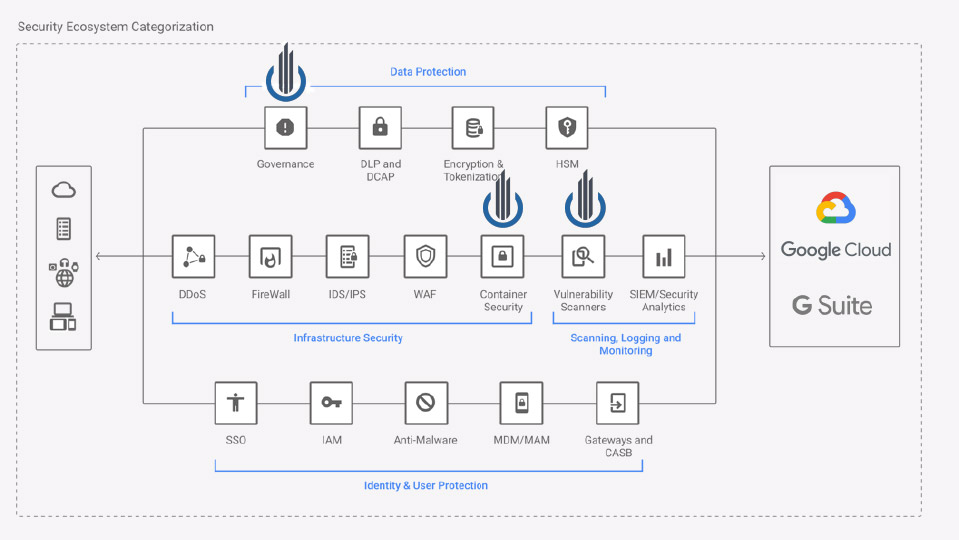
Google Cloud Security Command Center
Website: cloud.google.com/security-command-center
License: commercial
The Cloud Security Command Center helps security teams to collect data, identify threats and eliminate them before they harm the company.
As you can see from the name, Google Cloud SCC is a unified control panel into which you can integrate various security reports, asset accounting mechanisms and third-party security systems, and manage them from a single, centralized source.
The interoperable API offered by Google Cloud SCC facilitates the integration of security events from a variety of sources, such as Sysdig Secure (container security for cloud-native applications) or Falco (runtime Open Source security).
Layered Insight (Qualys)
Website: layeredinsight.com
License: commercial

Layered Insight (now part of Qualys Inc) is built on the concept of “embedded security.” After scanning the original image for vulnerabilities using statistical analysis methods and performing CVE checks, Layered Insight replaces it with an instrumented image that includes an agent in the form of a binary.
This agent contains runtime security tests to analyze container network traffic, I / O flows, and application activity. In addition, it can perform security checks defined by the infrastructure administrator or DevOps teams.
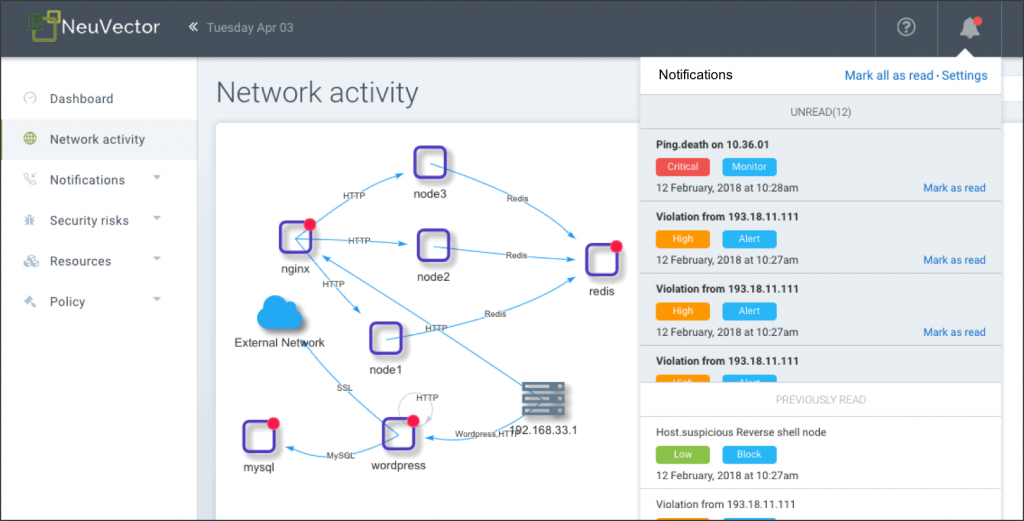
Neuvector
Website: neuvector.com
License: commercial
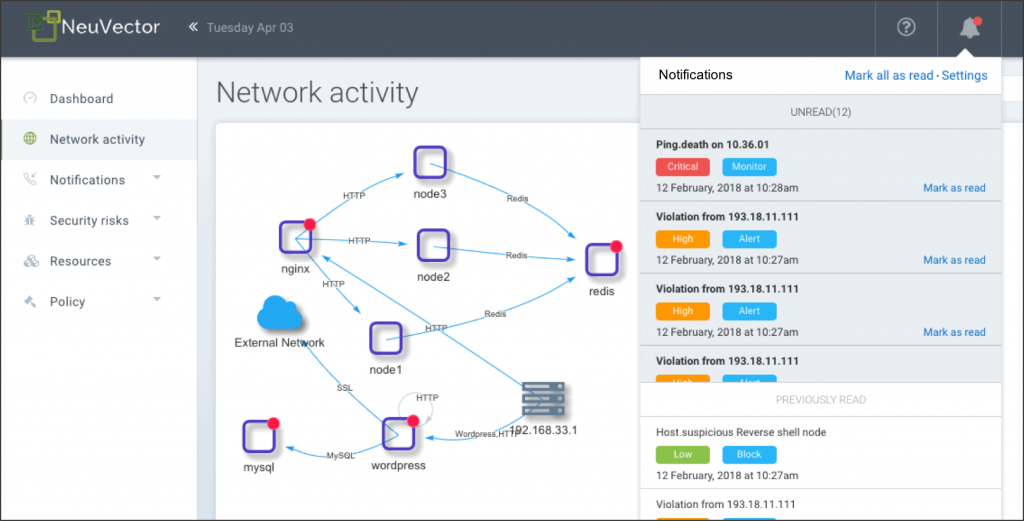
NeuVector conducts container security checks and provides runtime protection by analyzing network activity and application behavior, creating an individual security profile for each container. It can also independently block threats by isolating suspicious activity and changing the rules of the local firewall.
Network Integration NeuVector, known as the Security Mesh, is able to make a deep packet analysis and filtering at the 7th level for all network connections in the service mesh.
Stackrox
Website: www.stackrox.com
License: commercial
StackRox Container Security Platform tries to cover the entire lifecycle of Kubernetes applications in a cluster. Like other commercial platforms from this list, StackRox generates a runtime profile based on the observed behavior of the container and automatically creates an alarm for any deviations.
In addition, StackRox analyzes Kubernetes configurations using CIS Kubernetes and other rulebooks to evaluate container compliance.
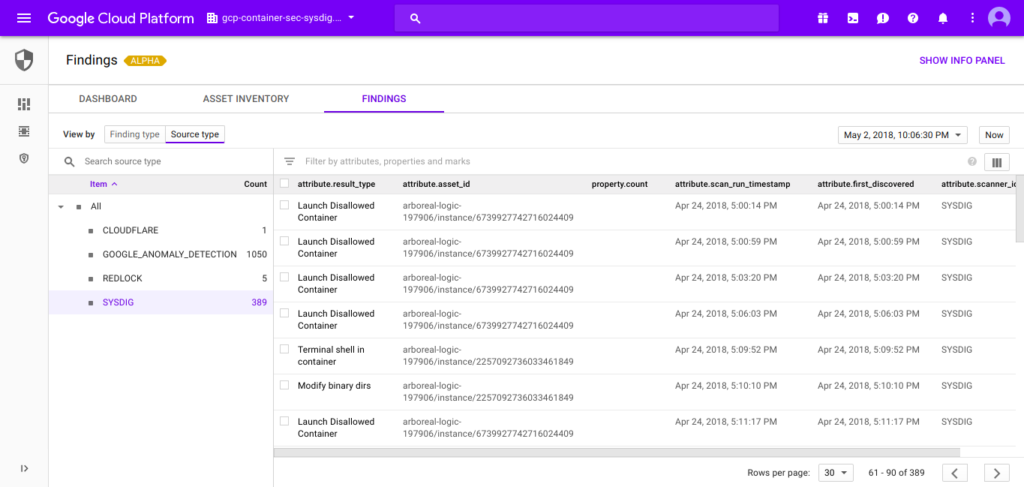
Sysdig secureq
Website: sysdig.com/products/secure
License: commercial
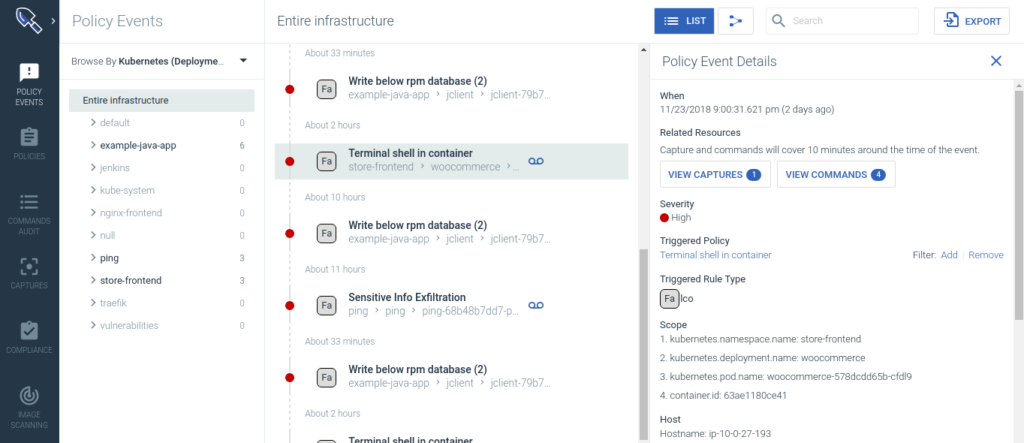
Sysdig Secure protects applications throughout the container and Kubernetes life cycle. It scans container images, provides runtime protection according to machine learning data and performs criminal examination to identify vulnerabilities, blocks threats, monitors compliance with established standards and audits activity in microservices.
Sysdig Secure integrates with CI / CD tools such as Jenkins and monitors images downloaded from the Docker registries, preventing in such way dangerous images from appearing in production. It also provides comprehensive runtime security, including:
- ML-based runtime profiling and anomaly detection
- runtime policies based on system events, the K8s-audit API, community projects (FIM – file integrity monitoring; cryptojacking) and the MITER ATT & CK;
- response and elimination of incidents.
Tenable container security
Website: www.tenable.com/products/tenable-io/container-security
License: commercial
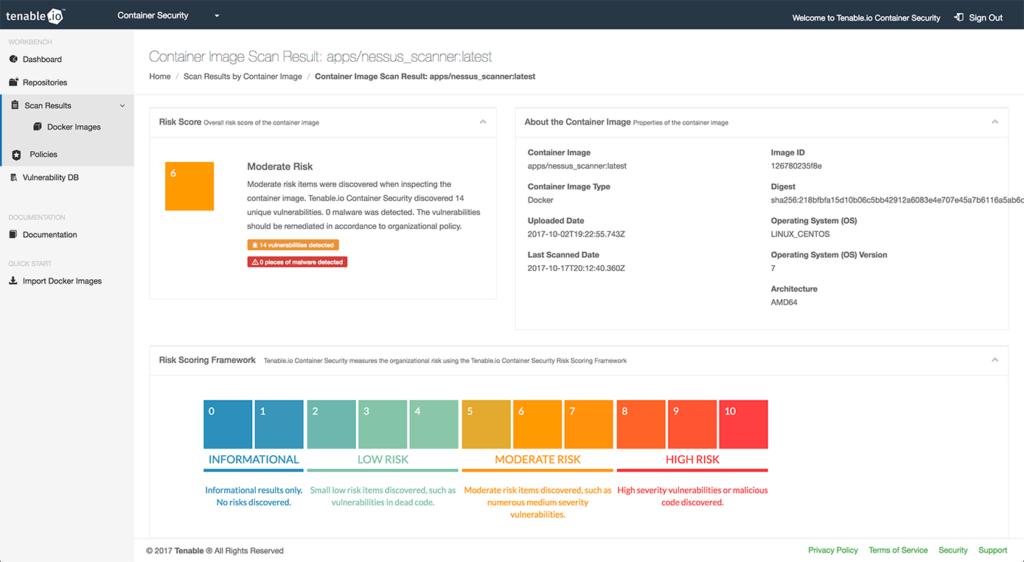
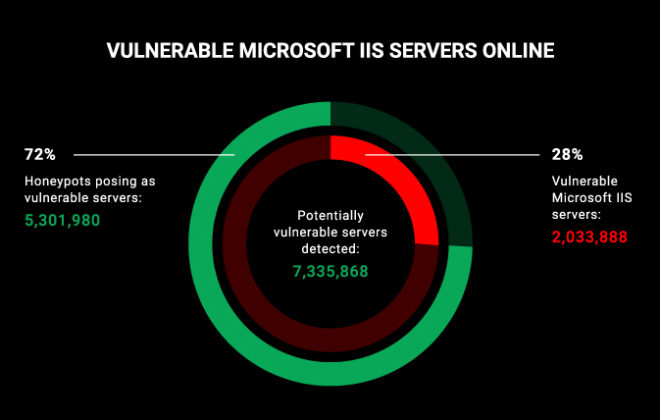
Till the introduction of containers, Tenable was widely known in the industry as the company that developed Nessus, a popular tool for searching for vulnerabilities and security audits.
Tenable Container Security uses its computer security expertise to integrate the CI / CD pipeline with vulnerability databases, specialized malware detection packages, and recommendations for resolving security risks.
Twistlock (Palo Alto Networks)
Website: www.twistlock.com
License: commercial
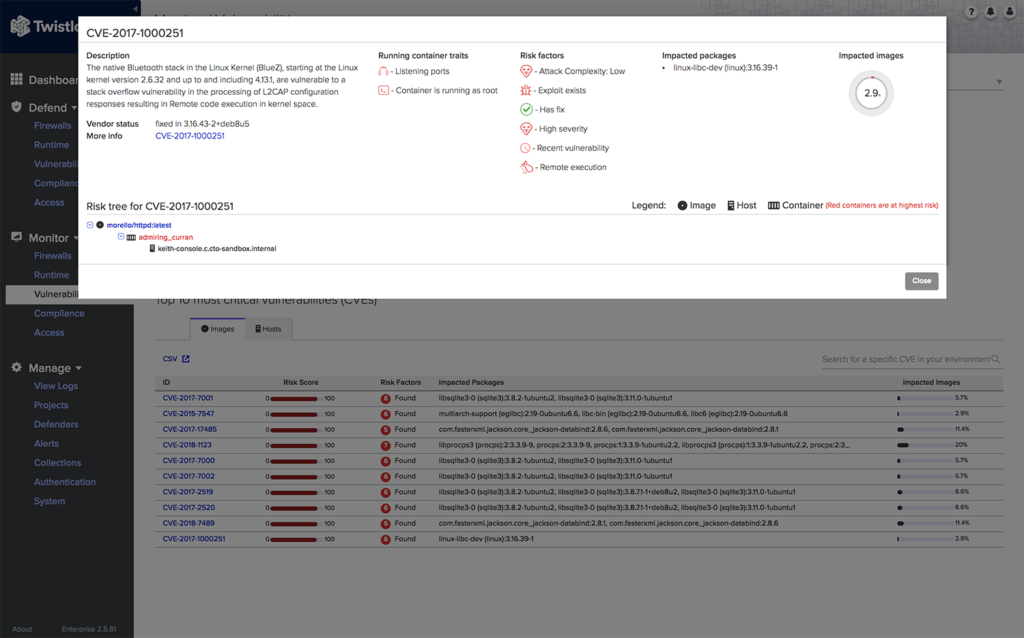
Twistlock promotes itself as a platform focused on cloud services and containers. Twistlock supports various cloud providers (AWS, Azure, GCP), container orchestrators (Kubernetes, Mesospehere, OpenShift, Docker), serverless runtimes, mesh frameworks and CI / CD tools.
In addition to conventional enterprise-level security methods, such as integration into a CI / CD pipeline or image scanning, Twistlock uses machine learning to generate behavioral patterns and network rules that take into account the characteristics of containers.
Some time ago, Twistlock was bought by Palo Alto Networks, which owns the Evident.io and RedLock projects. Till now is not known exactly how these three platforms will be integrated into PRISMA from Palo Alto.
Related Posts
Leave a Reply Cancel reply
Service
Categories
- DEVELOPMENT (123)
- DEVOPS (54)
- FRAMEWORKS (46)
- IT (25)
- QA (14)
- SECURITY (15)
- SOFTWARE (13)
- UI/UX (6)
- Uncategorized (8)