Runtime & Network Kubernetes security tools
Falco
Website: falco.org
License: free (Apache)
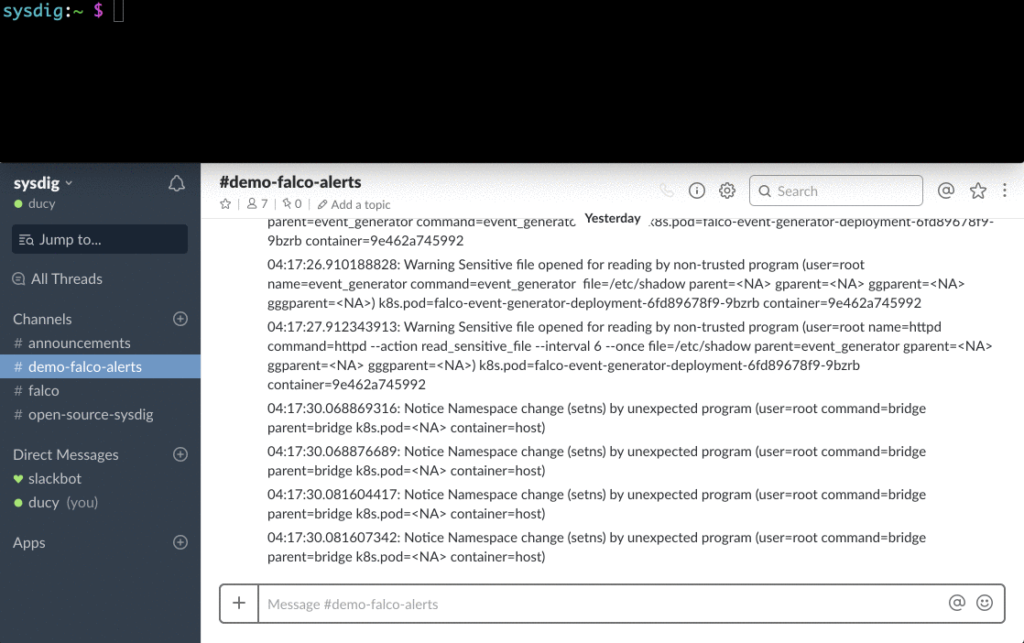
Using the Sysdig tools for working at the Linux kernel level and profiling system calls, Falco allows you to deeply immerse yourself in the behavior of the system. Its runtime rule engine is able to detect suspicious activity in Kubernetes applications, containers, base host and orchestra.
Falco provides complete transparency in runtime’s work and detection of threats by installing special agents on Kubernetes nodes for these purposes. As a result, there is no need to modify containers by embedding third-party code in them or by adding sidecar containers.
Linux security frameworks for runtime
These native Linux kernel frameworks are not “Kubernetes security tools” in the usual sense, but they deserve to be mentioned as an important element in the security context in runtime, which is included in the Kubernetes Pod Security Policy (PSP).
AppArmor connects the security profile to processes running in the container, defining file system privileges, network access rules, connecting libraries, etc. This is a Mandatory Access Control (MAC) based system. In other words, it prevents the execution of prohibited actions.
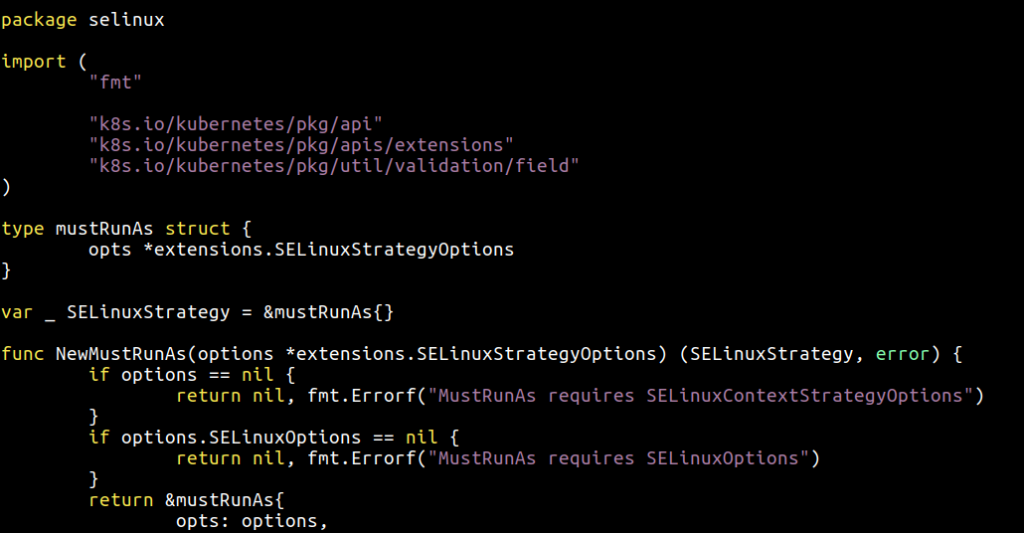
Security-Enhanced Linux (SELinux) is an advanced security module in the Linux kernel, in some aspects similar to AppArmor and often compared to it. SELinux is better than AppArmor in power, flexibility and subtlety of settings. Its disadvantages are prolonged development and increased complexity.
Seccomp and seccomp-bpf allow you to filter system calls, block the execution of those that are potentially dangerous for the basic OS and are not needed for the normal operation of user applications. Seccomp at some points is similar to Falco, although it doesn’t know the specifics of containers.
Sysdig open source
Website: www.sysdig.com/opensource
License: free (Apache)
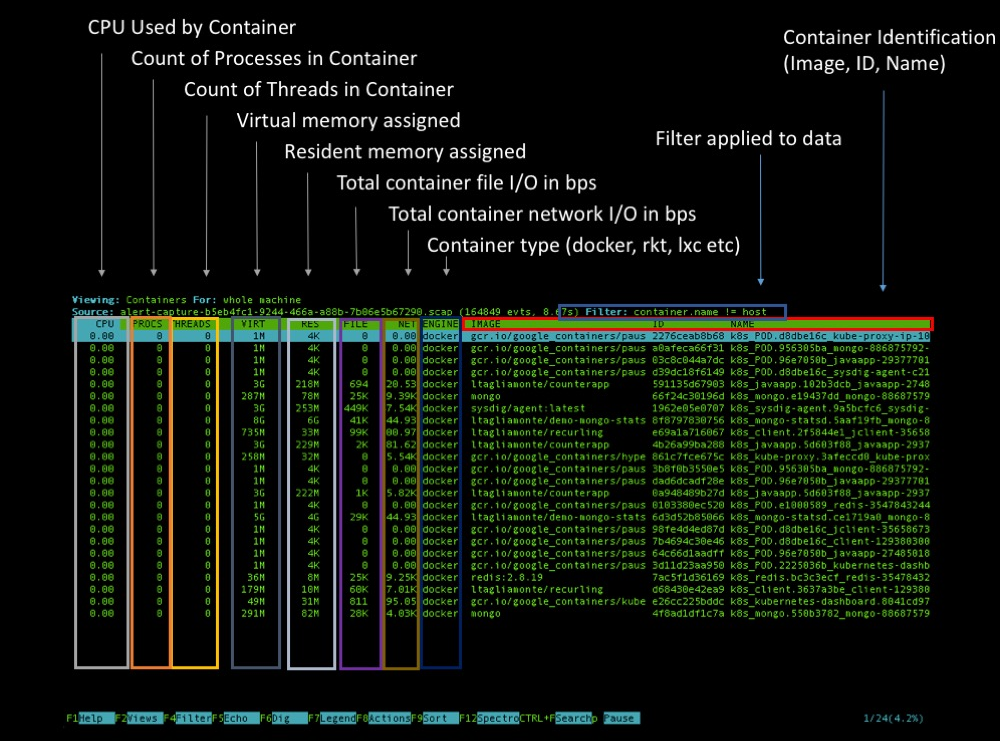
Sysdig is a complete tool for analyzing, diagnosing, and debugging of Linux systems (also works on Windows and macOS, but with limited features). It can be used to collect detailed information, check and forensics of the base system and any containers running on it.
Sysdig also natively supports container runtimes and Kubernetes metadata, by adding extra dimensions and labels to all the information gathered about system behavior. There are several ways to analyze the Kubernetes cluster using Sysdig: you can capture at a specific point in time via kubectl capture or run an interactive interface based on ncurses using the kubectl dig plugin.
Kubernetes Network Security
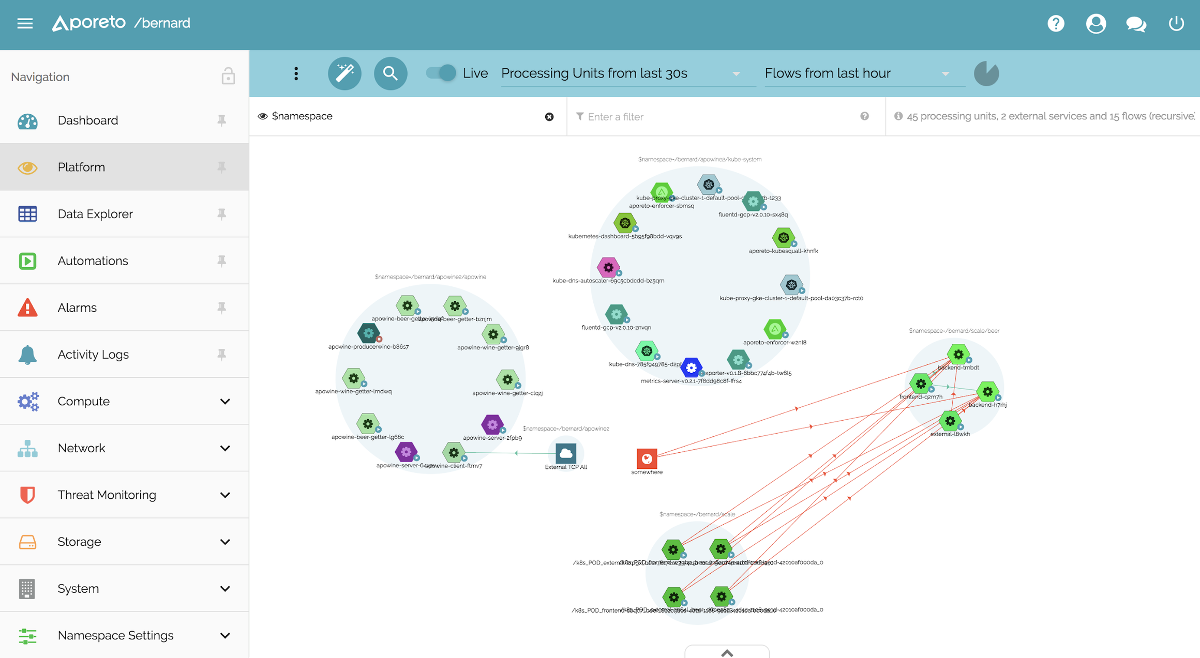
Aporeto
Website: www.aporeto.com
License: commercial
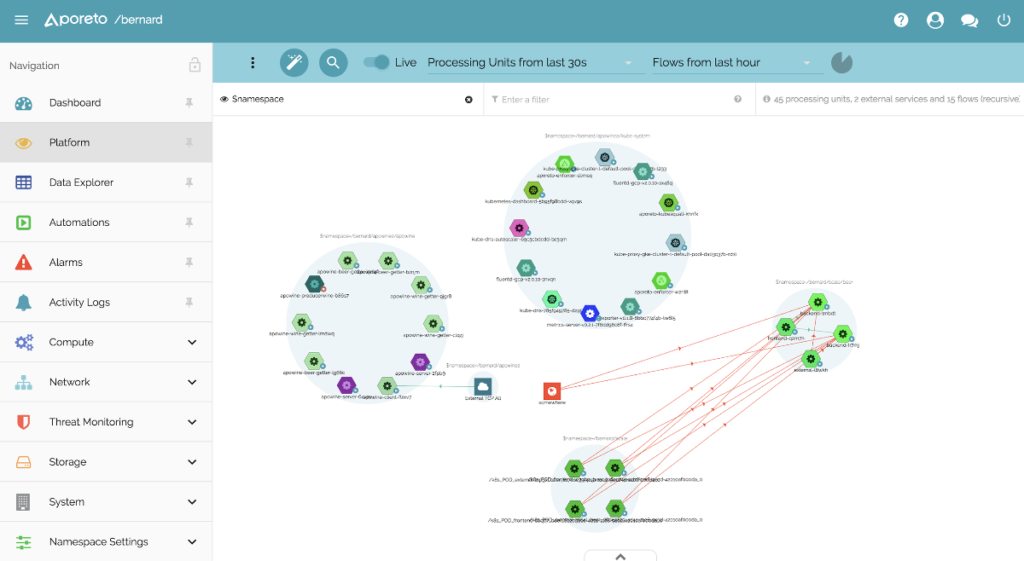
Aporeto offers “security separated from the network and infrastructure.” This means that Kubernetes services not only receive a local ID (ServiceAccount in Kubernetes), but also a universal identifier / fingerprint that can be used to securely verify interaction with any other service, for example, in an OpenShift cluster.
Aporeto is able to generate a unique identifier not only for Kubernetes / containers, but also for hosts, cloud functions and users. Depending on these identifiers and the set of network security rules set by the administrator, communications will be allowed or blocked.
Calico
Website: www.projectcalico.org
License: free (Apache)
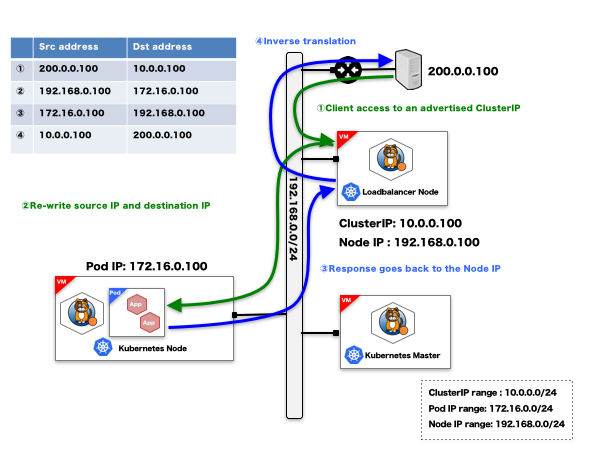
Calico is usually deployed during the installation of the container orchestrator, which allows you to create a virtual network for connecting containers. In addition to this basic network functionality, the Calico project works with Kubernetes Network Policies and its own set of network security profiles, supports endpoint ACLs (access control lists) and annotation-based network security rules for Ingress and Egress traffic.
Cilium
Website: www.cilium.io
License: free (Apache)
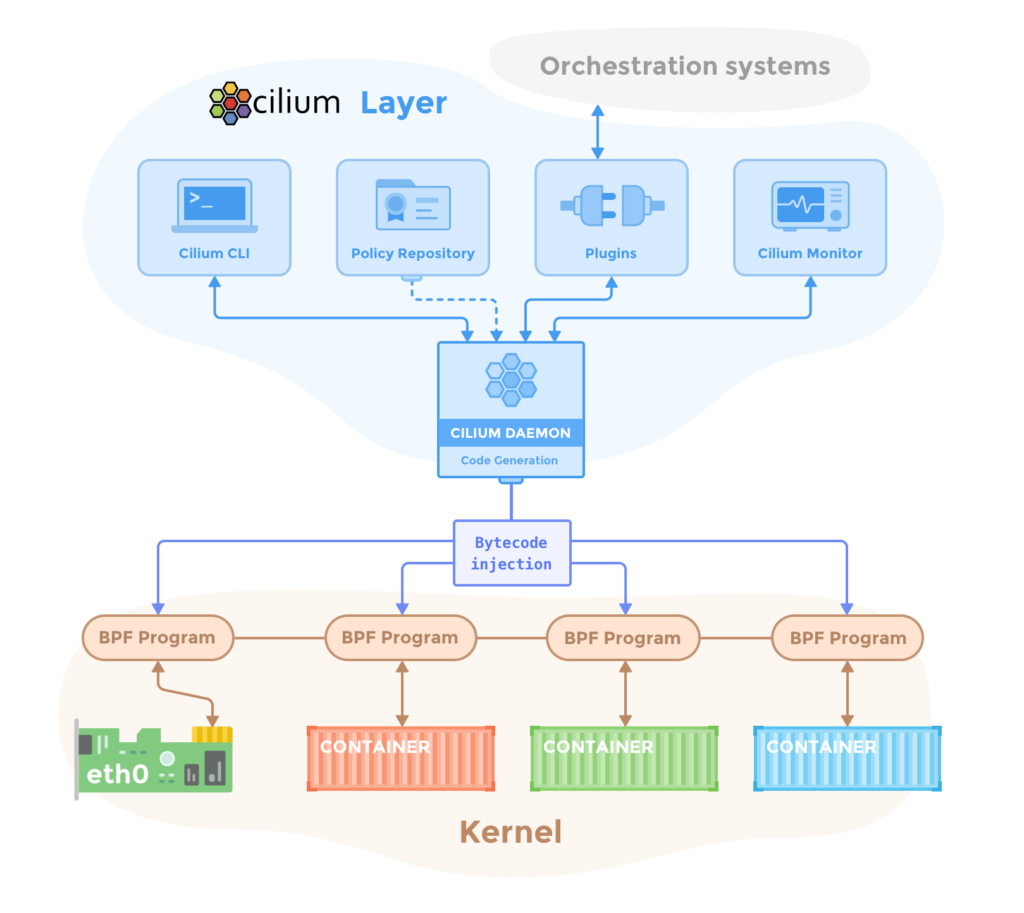
Cilium acts as a container firewall and provides network security features originally adapted to Kubernetes and microservice workloads. Cilium uses a new Linux kernel technology called BPF (Berkeley Packet Filter) to filter, monitor, redirect and adjust data.
Cilium is able to deploy container-based network access policies using Docker or Kubernetes tags and metadata. Cilium also understands and filters various 7-levels protocols, such as HTTP or gRPC, allowing you to define a set of REST calls that, for example, will be allowed between two Kubernetes deployments.
Istio
Website: istio.io
License: free (Apache)
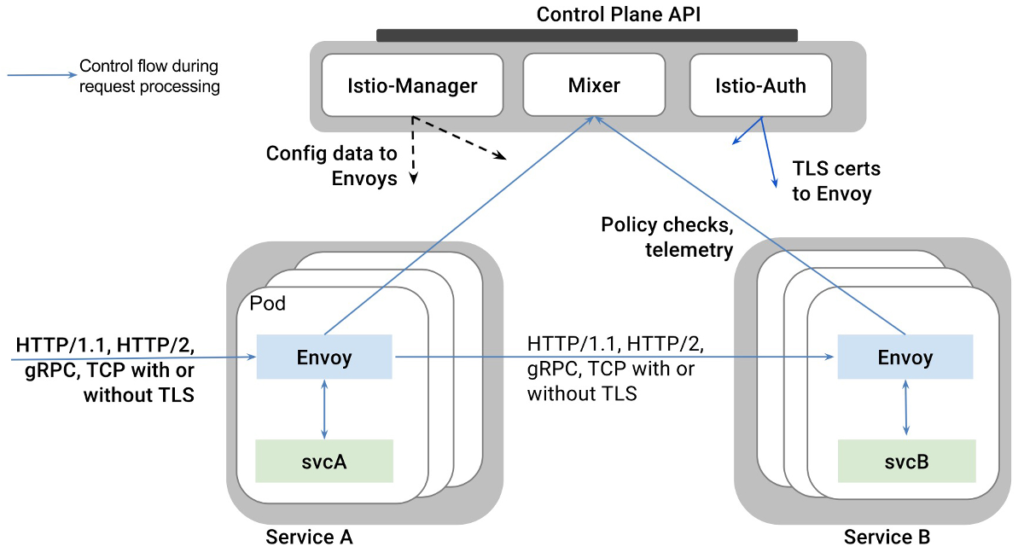
Istio is widely known as the implementation of the service mesh paradigm by deploying a platform-independent control plane and redirecting all managed service traffic through dynamically configured Envoy proxies. Istio takes advantage of this advanced view of all microservices and containers to implement various network security strategies.
Istio’s network security capabilities include transparent TLS encryption for an automatic upgrade of the communication protocol between microservices to HTTPS and its own RBAC system for identification and authorization to enable / disable the exchange of data between different workloads in the cluster.
Tigera
Website: www.tigera.io
License: commercial
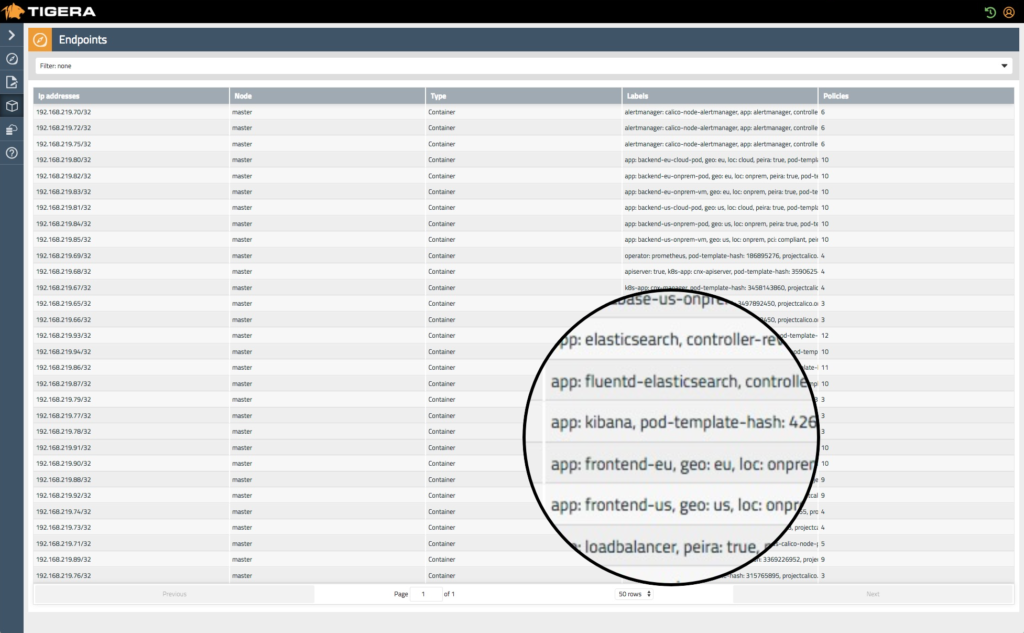
This solution, called the Kubernetes Firewall, focuses on a zero-confidence network security approach.
Similar to other native Kubernetes networking solutions, Tigera relies on metadata to identify various services and objects in the cluster and provides runtime problem detection, continuous network compliance and transparency of monitoring for multi-cloud or hybrid monolithic-containerized infrastructures.
Trireme
Website: www.aporeto.com/opensource
License: free (Apache)

Trireme-Kubernetes is a simple and straightforward implementation of the Kubernetes Network Policies specification. The most noteworthy feature is that – unlike similar Kubernetes network security products – it doesn’t require a central control plane to coordinate the mesh. This makes the solution trivially scalable. In Trireme, this is achieved by installing an agent on each node that connects directly to the host’s TCP / IP stack.
Related Posts
Leave a Reply Cancel reply
Service
Categories
- DEVELOPMENT (123)
- DEVOPS (54)
- FRAMEWORKS (46)
- IT (25)
- QA (14)
- SECURITY (15)
- SOFTWARE (13)
- UI/UX (6)
- Uncategorized (8)